A Ransomware Group Hacks Bet9ja Website
A Ransomware Group Hacks Bet9ja Website
In This Content
Bet9ja has been allegedly hacked by a ransomware group dubbed BlackCat. Although this has been yet to be confirmed by the betting giant, the activity has been made public as the said hackers made a statement about it according to another tech update platform.
https://twitter.com/ido_cohen2/status/1511673013250494464?s=20&t=LbVQUmvSe0oXIrmT4WmN9Q
In the early hours of Wednesday, April 6th, 2022., the giant betting platform Bet9ja went into a maintenance mode which is not unusual for them. Over the years the betting giant has taken it upon itself to run maintenance services over midnight when traffic on the website will be considered minimal.
Bet9ja has attributed the issue to maintenance taking extremely long and has advised their customers to relax as their transactions and funds are in place and safe.
As you can see in the tweet up there, Bet9ja isn’t the only victim in this current rampage, another betting company goldbet.it is on the receiving end and for a fact, the website is still currently down after an unusual amount of downtime.
About The Ransomware Group Dubbed BlackCat.
This group doesn’t have an online presence apart from an exclusive Onion site, where they post their activities, updates, and targeted victims.
Background
First observed in November 2021, ALPHV, also known as ALPHV-ng, BlackCat, and Noberus, is a ransomware-as-a-service (RaaS) threat that targets organizations across multiple sectors worldwide using the triple-extortion tactic.
Building upon the common double-extortion tactic in which sensitive data is stolen prior to encryption and the victim threatened with its public release, triple-extortion adds the threat of a distributed denial-of-service (DDoS) attack if the ransomware group’s demands aren’t met.
Demonstrating prior experiences in this threat space, such as the use of proven big-game hunter tactics, techniques, and procedures (TTP) and the apparent recent success, this threat was likely created by a former ransomware group member rather than a new-comer.
Going further, some cybercrime forum users have commented that ALPHV may even be an evolution or rebranding of BlackMatter, itself a ‘spin-off’ or successor of REvil and DarkSide.
Previously advertised on Russian-language cybercrime forums (Figure 1), affiliates are enticed to join the group with returns of up to ninety percent of any ransom collected.
Executive Summary
- CloudSEK’s Threat Intelligence Research team analyzed the profile of the ransomware group dubbed BlackCat.
- This group doesn’t have an online presence apart from an exclusive Onion site, where they post their activities, updates, and targeted victims.
- BlackCat is the first known professional ransomware group to use the Rust programming language.
- CloudSEK’s Threat Intelligence team conducted further research to analyze the group’s operations and Tactics, Techniques, and Procedures (TTPs).
Victimology
As is common with big-game hunter ransomware threats, victims are typically large organizations from which bigger ransoms can be extorted with reports suggesting that demands have ranged from US$400K up to $3M payable in cryptocurrency.
Whilst the true number of victims is unknown, over twenty organizations have been named on the group’s Tor ‘leak site’, across a variety of sectors and countries including:
- Australia, Bahamas, France, Germany, Italy, Netherlands, Philippines, Spain, United Kingdom, and the United States.
- Business services, construction, energy, fashion, finance, logistics, manufacturing, pharmaceutical, retail, and technology.
Detailed Analysis
Information from the BlackCat Onion Site
- BlackCat, also known as ALPHVM, is a newly emerged ransomware group that maintains a presence on the dark web. They are currently linked to two different websites, a leak site called ALPHVM and BlackCat.
Information from the Social Media
- BlackCat has garnered a lot of attention on Twitter for being a Rust-based ransomware group. One of the initial groups of threat actors that used Rust as a part of their arsenal was the BadBeeTeam Ransomware.
- Some Twitter users such as Dark Tracers mention that BlackCat has four Onion sites in operation.
- There are various speculations on who the operators behind such a complicated malware could be. However, researchers along with some notorious threat actors, claim that the BlackCat ransomware group operators were formerly associated with the REvil ransomware group.
Information from Discussions on Cybercrime Forums
- ALPHV was a former member of the REvil group, which suggests that the BlackCat ransomware group is most likely associated with the REvil ransomware group.
- A member of the LockBit ransomware group has claimed that BlackCat is the rebranded version of BlackMatter/ DarkSide.
- Besides, there are discussions on how the group used Russian cybercrime forums to recruit affiliates to work with them. They are also keen on hiring pentesters skilled in Windows, Linux, and ESXi, which are their encryption targets.
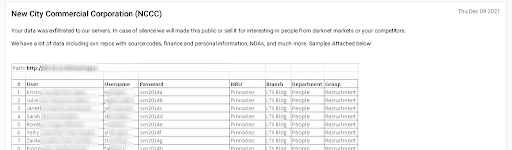
- CloudSEK’s Threat Intelligence team picked up similar recruitment posts that were published between 8 December 2021 to 12 December 2021. The posts mention that the partners will receive 80%-90% of the final ransom amount, obtained through double extortion.
- Even months prior to the emergence of the BlackCat ransomware, the book ‘Black Hat Rust’ was distributed across cybercrime forums, and accesses to ESXi devices was being actively traded.
- So far, the list of victims affected by Alphv-ng/ BlackCat ransomware are:
- Star World Wide (Posted on 30 November 2021)
- New City Commercial Corporation (Posted on 9 December 2021)
- A threat actor on an English cybercrime forum recently requested affiliates and access from selected countries. The actor’s profile picture and the profit percentages being offered indicate that they could be operators or affiliates of the BlackCat ransomware group.
- The actor has requested access to entities from the following countries:
- United States
- Ukraine
- Switzerland.
- They have also shared a rate card for potential affiliates to consider:
References
https://github.com/CyberSoldiers/IOCs/blob/main/BlackCat_Ransomware
https://twitter.com/EcuCERT_EC/status/1471506980413997071


